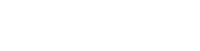
On Windows Server 2008 (and Vista/Windows 7) there are three types of firewall profiles—Domain, Private, and Public.
You can set a Firewall state(rules) for each profile and each firewall profile applies depending on your network location. This let you set different firewall rules depending on your network location:
Microsoft basically defines these as:
Domain Profile – applied automatically when your server is connected to an Active Directory domain.
Private Profile – you can assign this profile manually when your server is connected to any private address (10.200.xxx.xxx, etc.)
Public Profile – applied by default when you first connect the server to any unknown network. Other than domain networks, all networks are initially categorized as Public.
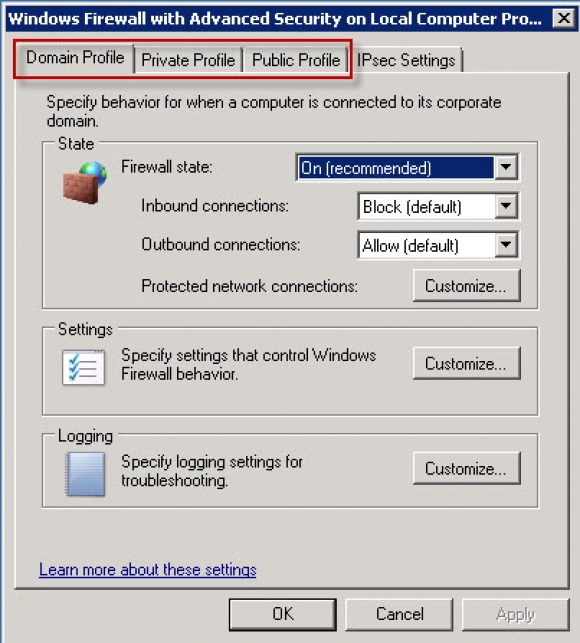
Although Microsoft offers the above definitions, in the case of a Web Server, often your actual connection type will be “Public” even if you are connected to an Active Directory domain.
To verify what your current connection is classifed as, open Windows Firewall and it will be displayed in the Network Location field:
You can configure any profile, even one that is not currently being applied. If you do not alter profile settings, their default values are applied whenever Windows Firewall with Advanced Security uses the profile. We recommend that you enable Windows Firewall with Advanced Security on all three profiles.
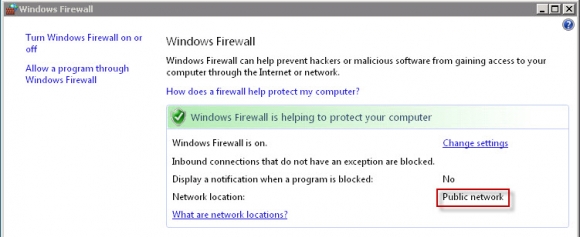
If you are troubleshooting a firewall rule problem: you will want to ensure that the firewall rule you are trying to get working is enabled on the correct profile. You can verify the settings in the ‘Windows Firewall with Advanced Security‘ panel:
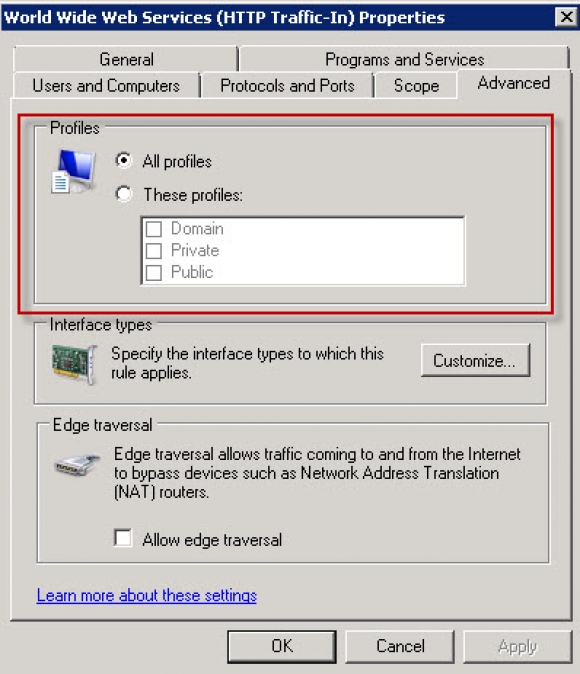
If you need to adjust the profile the rule is enabled on, double-click the rule, and under the ‘Advanced‘ tab you can edit which profiles the rule applies to:
Content retrieved from: https://support.appliedi.net/kb/a318/windows-server-2008-firewall-profiles.aspx.